Hello, my loyal band of cyber sentinels. Today, we’re tackling a topic that hits close to home for yours truly: securing remote work environments. Now, as the Grumpy CISO who’s been navigating the digital seas from the comfort of my own home office, I can tell you firsthand that this is a subject near and…
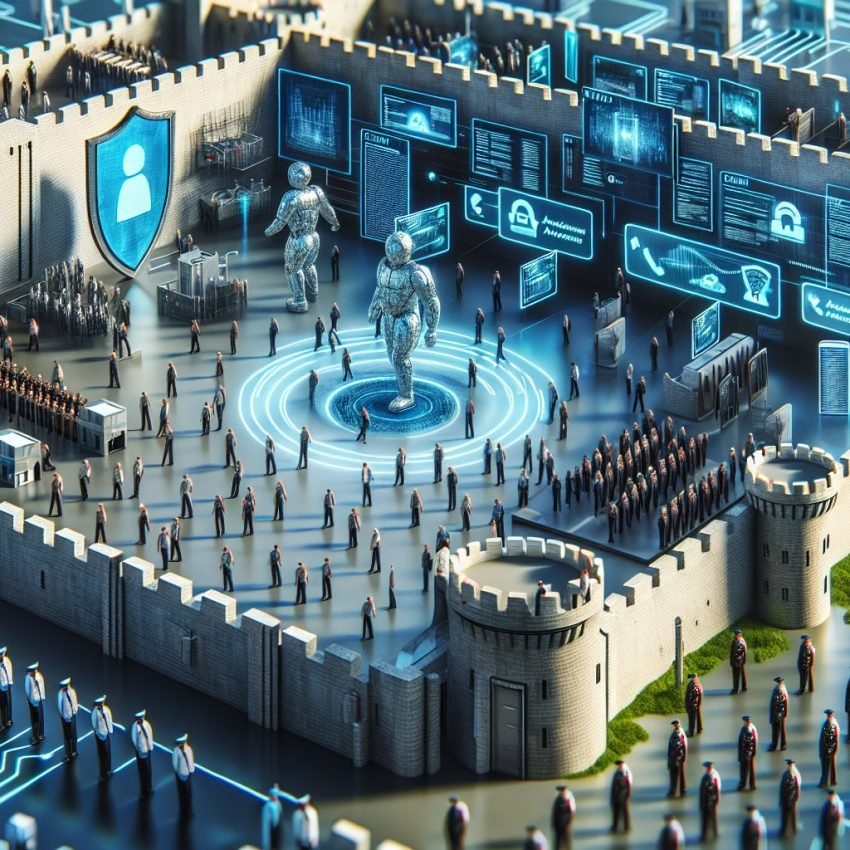
Identity & Access Management: The Gatekeepers of the Digital Fortress
Welcome back, my fellow defenders of the digital realm. Today, we delve into a topic that could make even the grumpiest CISO appreciate the finer points of security architecture: Identity and Access Management, or IAM. Imagine our digital fortress, teeming with valuable data and critical systems, protected not just by walls and moats but by…
Single Sign On: The Key to the Fortress
Good day, my fellow digital sentinels. Today we’re diving into a topic that, for once, brings a smile to the face of even the Grumpiest CISO: Single Sign-On (SSO). In the perilous landscape of cybersecurity, SSO stands as a beacon of simplicity and security, offering a centralized authentication source that allows our digital fortresses to…
Smart Devices, Serious Threats: Navigating the Security Challenges of IoT
Good day, followers of the Grumpy CISO. Today, I want to touch on a scenario that might sour even the most cheerful CISO’s mood: imagine having all your data stolen by your refrigerator. Yes, you heard me right, and no, that wasn’t a slip of the tongue. In our current era of technological ubiquity, almost…
What Happened to My Phone: An Introduction to SIM Swapping Attacks
High on the list of things that make me a Grumpy CISO is the widespread reliance on SMS as a security tool. In the digital fortress that is modern cybersecurity, SMS-based authentication often feels like a flimsy gate, swinging in the breeze and inviting trouble. It’s exactly this kind of vulnerability that paves the way…